ShieldRisk AI
Sovereign Audit Trust Certificate
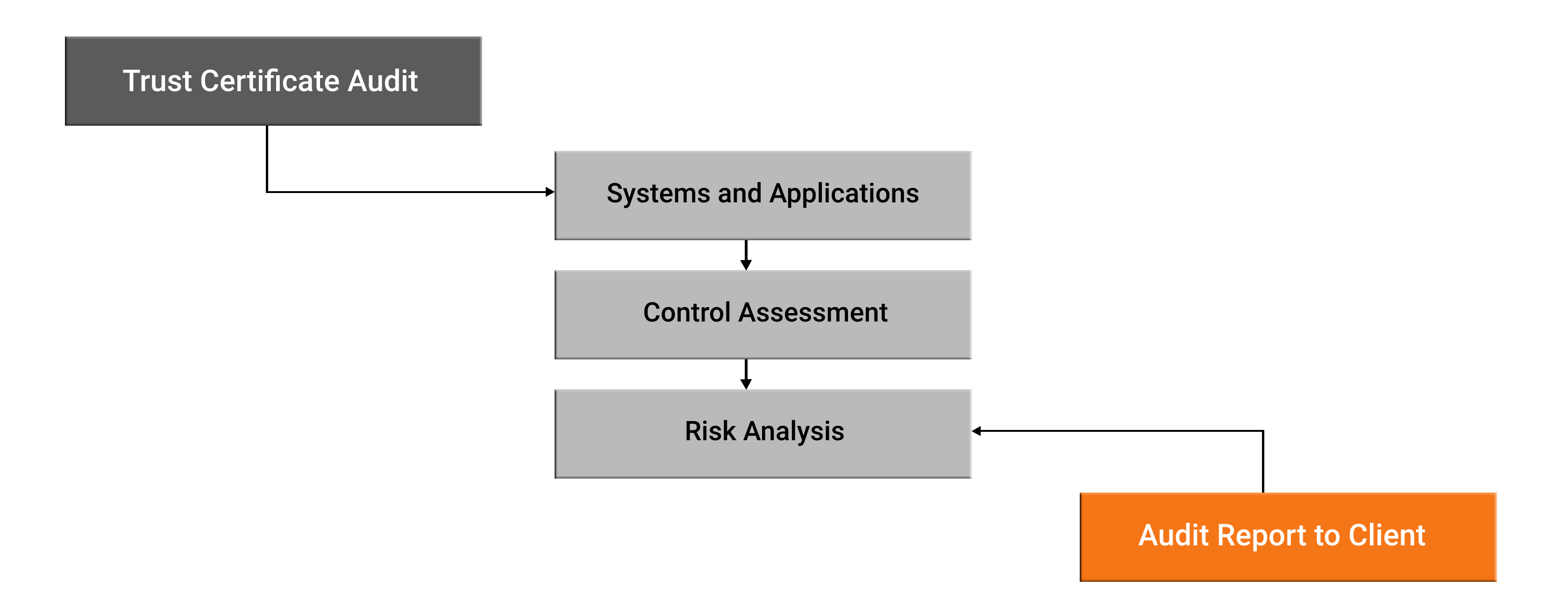
Independent Oversight of the Management of Risks inherent in the Vendor Organization’s Actions, Events, and Security controls


ShieldRisk Trust Certificate
Independent Audit and Compliance Audit for Technical and Organizational controls evaluation by Governance, Risk, and Compliance Professionals

ShieldRisk
Independent Audit Report
A proactive approach to Independent Audit for SaaS software, ERP systems, and Services provided by Organizations.
Independent Audit Report sharing aptitude with current and prospective clients demonstrating adherence to Legal, Data Security, and Information Security Compliance.
Unified platform for Third-party Vendor Risk Management
ShieldRisk empowers a Strategic Risk-based approach for Vendor Management in Compliance with the Global Security standards & efficacy for the services provided by the third-party Service Providers.

Data Privacy
Protection of personally identifiable Information and Security of Data

Technical Vulnerability
Technical Vulnerabilities of Systems Applications, assets, and network

Process Integrity
Process Integrity of confidential Information and valid preservation

Cyber Threat
Cyber Threat Intelligence of actors, sources, and Technical Intelligence
Regulatory Compliance
Profound coverage of Data Security Global Regulations and Compliance

Cloud Security
Cloud Data storage Security for Critical data and Information systems
Connect With Us
+91-8779784050 | +1 551-307-7576
reachus@shieldrisk.ai
Assess Third-Party Vendor
Connect with our GRC Expert for Vendor Risk Assessment and Due Diligence
