ShieldRisk AI is an AI-powered third-party risk management (TPRM) platform that enables organizations to continuously identify, assess, monitor, and report cyber and compliance risks arising from vendors, suppliers, and external partners.
India’s first comprehensive and leading TPRM with AI, Attack Surface Monitoring & BGV for vendor companies
What ShieldRisk AI Does
Key Capabilities
- AI-driven third-party and vendor risk assessments
- Automated risk questionnaires and evidence collection
- Continuous vendor risk scoring and monitoring
- Regulatory-aligned dashboards and audit-ready reports
How ShieldRisk AI Works
Regulatory Alignment
- Reserve Bank of India (RBI) Cybersecurity Framework
- SEBI Cyber Security and Cyber Resilience Framework (CSCRF)
- ISO/IEC 27001 and ISO/IEC 27701 vendor risk requirements
- CERT-In cybersecurity guidelines
Who Uses ShieldRisk AI
Why Shieldbyte Infosec
ShieldRisk AI is developed and operated by Shieldbyte Infosec, a CERT-In empanelled cybersecurity organization providing audits, consulting, and AI-driven cybersecurity platforms to enterprises and regulated organizations.
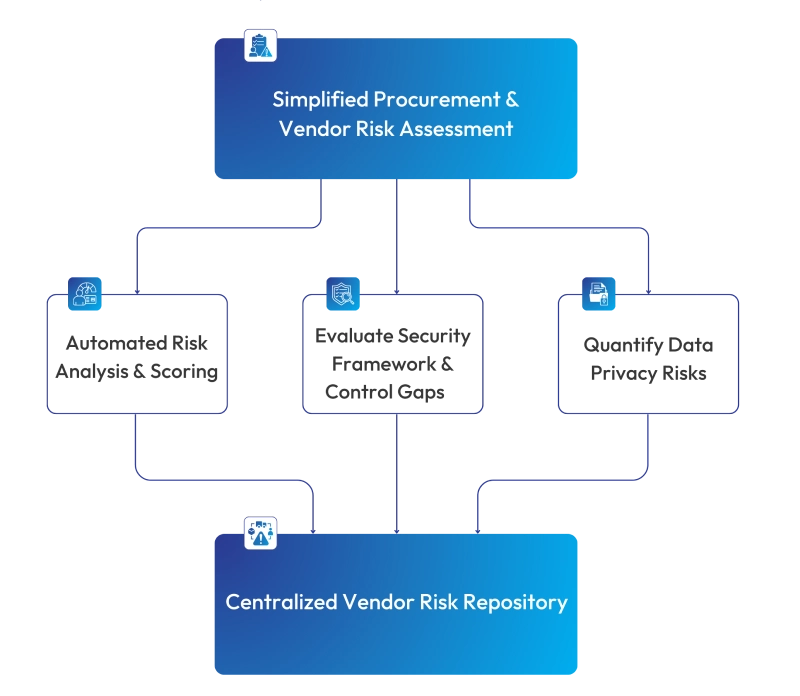
Vendor Risk Assessment
Challenges & Standardized Framework
Organizations often struggle with fragmented vendor assessments, relying on spreadsheets and manual efforts. The variations in vendor services, data privacy frameworks, and lack of centralized visibility make it difficult for teams to assess and mitigate vendor-related risks effectively. Some common challenges are
Disjointed Data Sets
Vendor information is scattered across multiple spreadsheets without a standardized assessment framework.
Diverse Vendor Privacy Practices
Vendors handling different types of personal and confidential data (PII, PHI, financial) require tailored assessments.
Manual Risk Analysis Processes
Evaluating security frameworks and control effectiveness manually leads to delays and oversight.
Resource-Heavy Assessment Cycles
Procurement, Quality, and Audit teams face repetitive, time-consuming efforts to assess each vendor.
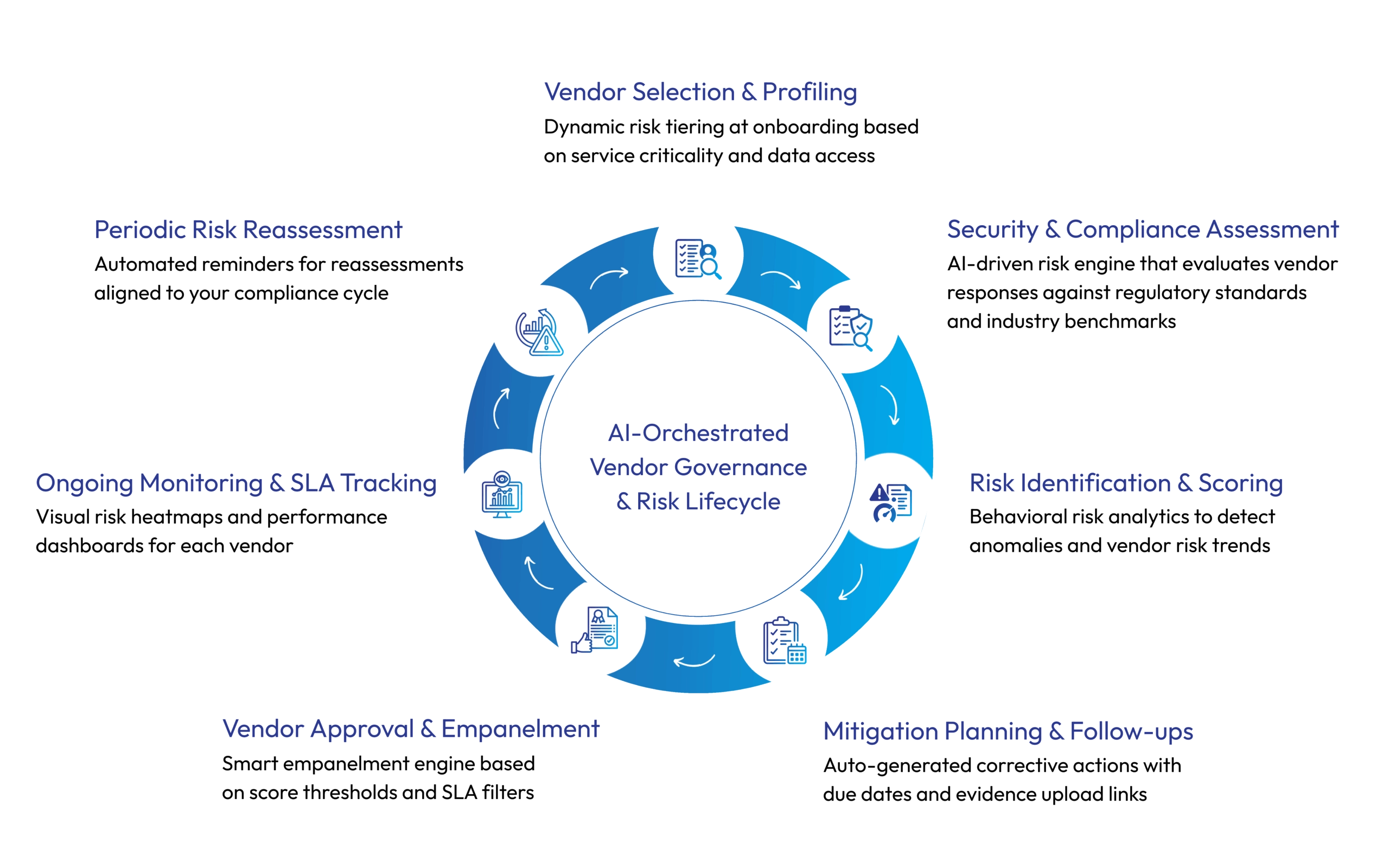
AI-Orchestrated
Vendor Governance & Risk Lifecycle
Empower your enterprise with innovative Vendor Governance & Risk Lifecycle management, assess, monitor, and mitigate third-party risks with confidence. Turn compliance into a competitive advantage.
Toward Continuous Trust
Beyond Risk Identification
ShieldRisk is not just a platform; it’s a Third-Party Risk Governance Ecosystem designed to help you:
Reduce Vendor Risk by >40% within 6 months
Identify hidden vulnerabilities and reduce third-party risk exposure by over 40% within six months.
Save hundreds of man-hours annually
Eliminate repetitive tasks and save hundreds of hours yearly through intelligent workflow automation.
Stay audit-ready across multiple regimes
Ensure continuous audit-readiness with structured evidence, automated logs, and mapped control validations.
Automate 80% of assessments and Tracking
Automate vendor assessments, follow-ups, and documentation—saving time and minimizing manual intervention.
Go Beyond Static Scores
Make Informed, Context-Aware Decisions
Unlike traditional platforms that rely solely on self-assessments or external ratings, ShieldRisk combines behavioral analytics, real-time regulatory mapping, and domain-specific intelligence to deliver scores that matter in context
We Serve Globally
Enterprise-Ready Features
Unlock powerful enterprise-ready features designed for scale, security, and compliance. From advanced access controls to seamless integrations, manage third-party risk with confidence across your entire ecosystem.